This Week in Matrix 2020-03-20
2020-03-20 — This Week in Matrix — Ben Parsons🔗Matrix Live 🎙
Matrix Live S04E30 - Matthew updates on Synapse perf, P2P and new Jitsi
🔗Dept of Spec 📜
anoa announced:
Here's your weekly spec update!
🔗MSC Status
Merged MSCs:
- No MSCs were merged this week
MSCs in Final Comment Period:
New MSCs:
- MSC2463: Exclusion of MXIDs in push rules content matching
- MSC2461: Proposal for Authenticated Content Repository API
🔗Spec Core Team
Next week the Spec Core Team is focusing MSC2432 (alias changes), MSC2451 (remove query_auth), and implementation.
🔗Dept of Servers 🏢
🔗Dendrite / gomatrixserverlib
Neil Alexander announced:
- P2P work is continuing at
p2p.riot.im, with various fixes and a new public room directory- Room version work is continuing with new headered event support in Kafka, the internal APIs and the sync API in Dendrite, and in the event code in gomatrixserverlib
- Joining rooms over federation is a bit more reliable now, as prev events are handled properly in this case and therefore the first message into the room doesn't get lost
- Some improved error handling work has been merged - thanks to prateek2211 and abbyck
- The
/joined_roomsendpoint is now implemented - thanks to prateek2211
Notes on usage:
In order to try p2p.riot.im, do I need to create an account or should I be signing in to some user?
Just register as normal. Be aware you are registering into your local in-browser Homeserver, rather than a remote service.
Neil Alexander also mentioned:
We've also created #homeservers-dev:matrix.org as a general non-implementation-specific channel for homeserver developers :-)
🔗matrix-media-repo
TravisR offered:
v1.1.0 has been released with experimental (incomplete) IPFS support, memory leak fixes, and other improvements. This is a highly recommended upgrade if you use
expireAfterDaysor have memory problems.
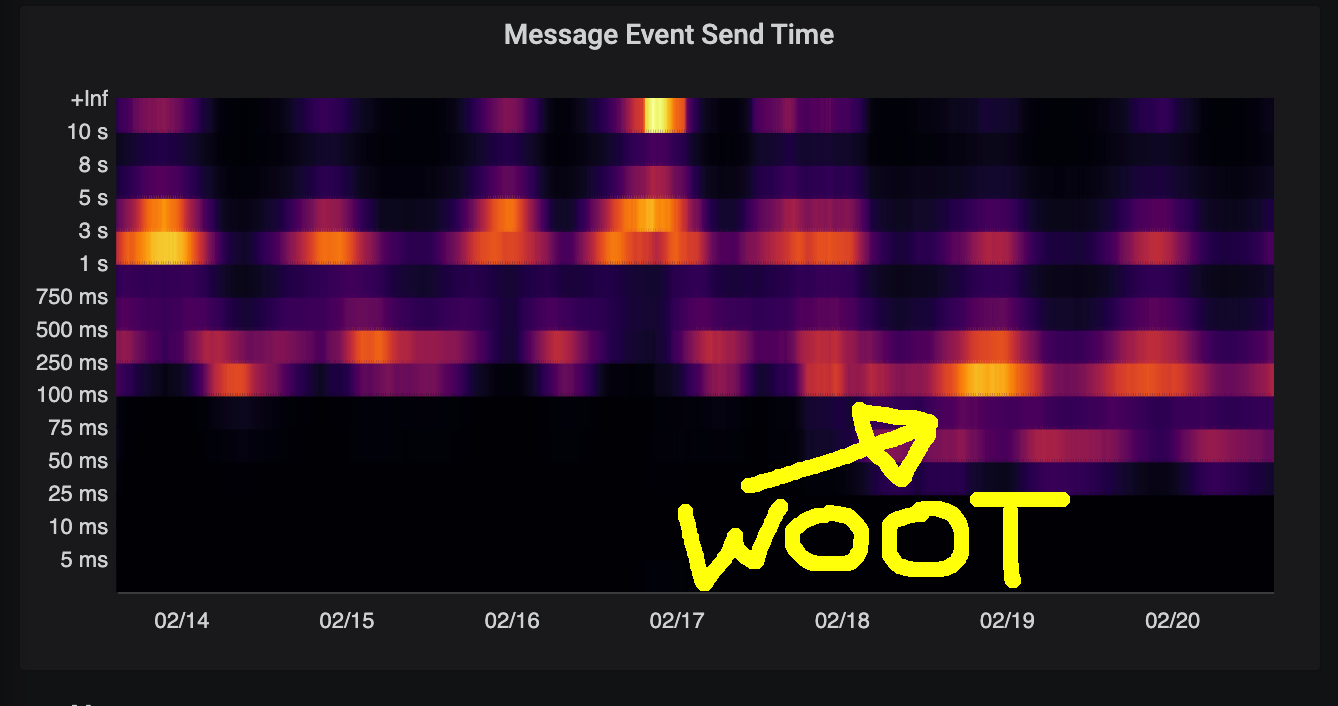
🔗Synapse
Neil reported:
This week we have seen a huge increase in traffic and so we are spending a lot of time battling with scaling. Most notably we shipped an optimisation to improve state resolution for room versions > 1. Our sharding effort continues and we are working towards backing matrix.org with redis for pub sub which is prerequisite for the project.
Aside from that we had some problems with push reliability, this should now be fixed. Sorry if you were bitten!
We also put out 1.12.0rc1 expect a full release early next week.
Next week performance performance performance. We’ll also complete improvements to user Interactive Auth for SSO installations.
🔗Synapse Deployments
Mathijs told us:
The docker image for synapse v1.12.0rc1 is now on mvgorcum/docker-matrix:v1.12.0rc1
🔗Dept of Bridges 🌉
🔗Welcome Christian!
Welcome to Christian, who is joining the Bridges team as an employee. He'll start out on the Slack bridge but will be working more generally with Half-Shot on all bridges.
🔗mx-puppet-bridge
mx-puppet-bridge is a general bridging library that supports (double)bridging and relays. The goal is to make it as easy as possible for others to bridge new third-party protocols to matrix. Support room Donate
sorunome told us:
- add adminme thanks to dhmf
- more tests
- unified namespaces!
Unified namespaces is a big update! This means that, if the remote protocol has globally unique IDs (e.g. as discord has the case) it will only create one room on matrix for any amount of puppets. Combining this with the advanced relay option, this means that protocol implementations (e.g. discord) now can act like a normal relay bridge only with super awesome puppeting! As in, the for the puppets, the DMs work and channels&guilds that the relay bot is not in. All this is possible without any changes to the protocol implementation, should the protocol have unique global IDs.
🔗Dept of Clients 📱
🔗Quotient / Quaternion SSO support
kitsune told us:
In preparation to the upcoming (long-awaited) releases for Quotient and Quaternion, the library has gained full-blown support of SSO flow, such as the one used by the Mozilla's homeserver, and adventurous Mozilla Matrix users can use the master branch of Quaternion to login to their accounts. Next step - official releases and backports.
🔗gomuks
Tulir said:
gomuks now supports markdown formatting in rainbow messages.
Or if you prefer:
gomuks now supports markdown formatting in rainbow messages.
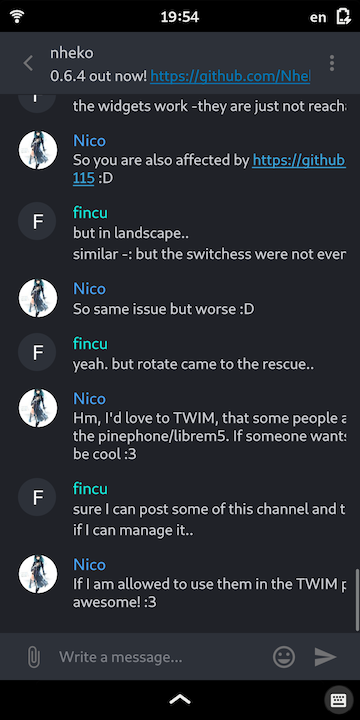
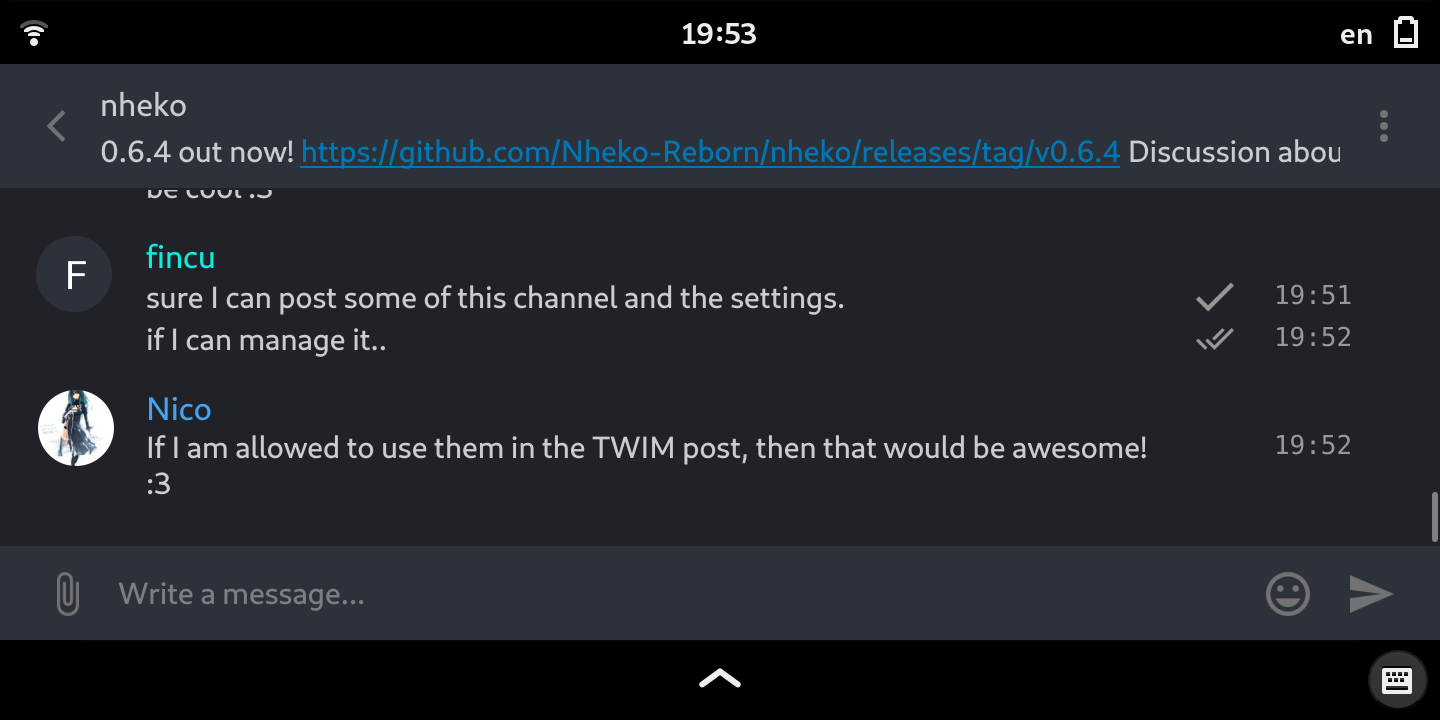
🔗Nheko
Nheko is a desktop client using Qt, Boost.Asio and C++17. It supports E2EE (with the notable exception being device verification for now) and intends to be full featured and nice to look at
Nico (@deepbluev7:neko.dev) told us:
Emi added a new sorting method to the room list, that keeps rooms with unread messages on top, even when the messages are older than the messages in silenced or read rooms. It makes the room list a lot nicer to use and after being skeptical at the start, I now use it on all my systems. Huge thanks to Emi for bearing with my long and confusing review!
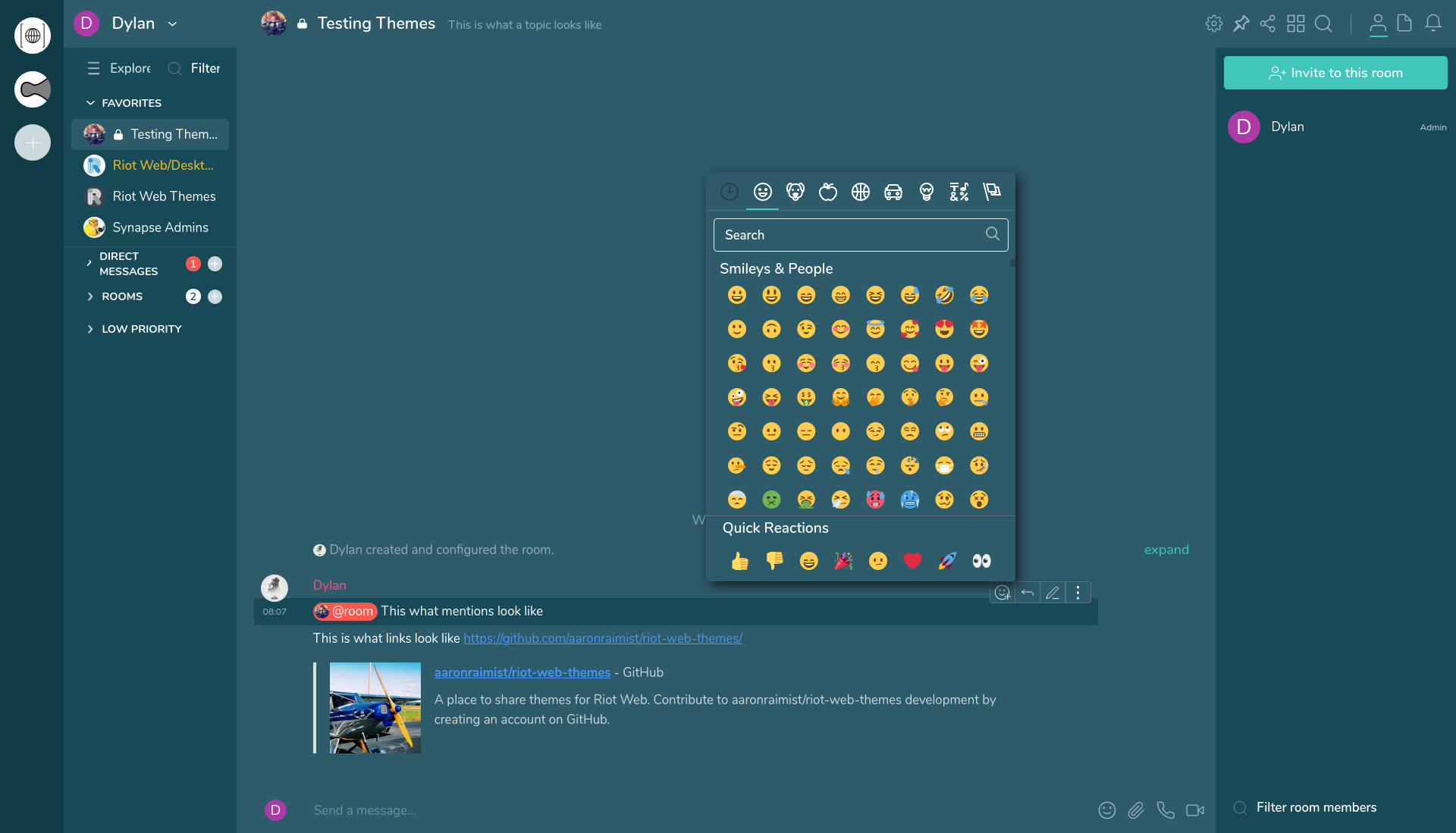
🔗Riot Web
Ryan reported:
- Keyboard shortcuts are more discoverable with a help popup that explains them
- Jitsi support for voice and video is moving into Riot itself (the integration manager is no longer used for this)
- Self-hosted Riots can be configured to use a different Jitsi server if desired
- Encrypted messages are faster to encrypt and send
- The room directory server selector has been reworked and is much easier to use and understand
- Many cross-signing polish fixes continue to land, hoping to ship cross-signing in a few weeks
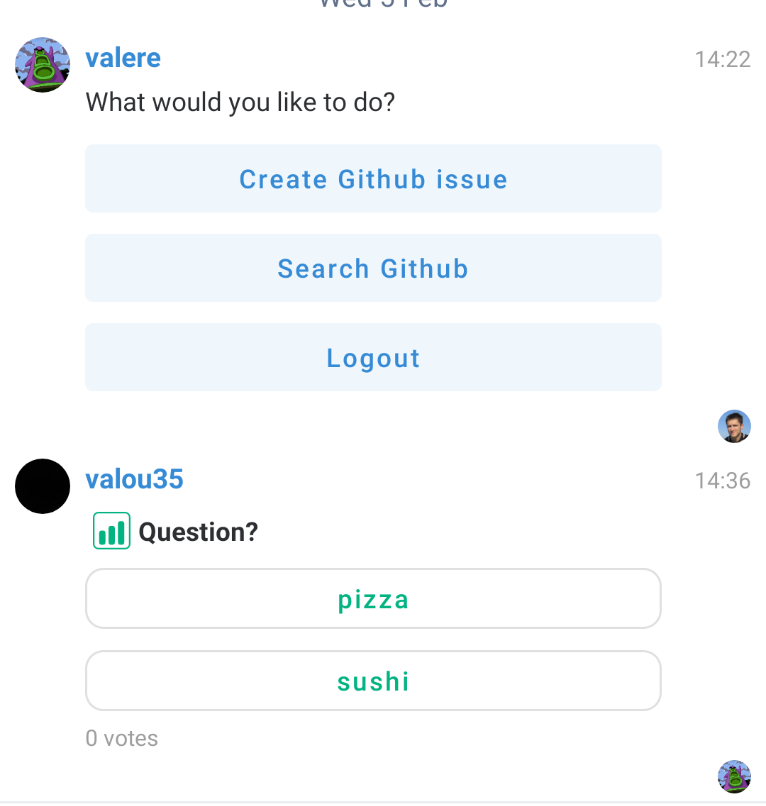
🔗RiotX, Quick corrective release 0.18.1
valere told us:
Improvements 🙌:
- Implementation of /join command
Bugfix 🐛:
- Message transitions in encrypted rooms are jarring #518
- Images that failed to send are waiting to be sent forever #1145
- Fix / Crashed when trying to send a gif from the Gboard #1136
- Fix / Cannot click on key backup banner when new keys are available
🔗Riot-iOS
Manu told us:
We are still working on cross-signing. QR code screens have landed on develop like storing and gossiping of cross-signing private keys.
🔗Dept of SDKs and Frameworks 🧰
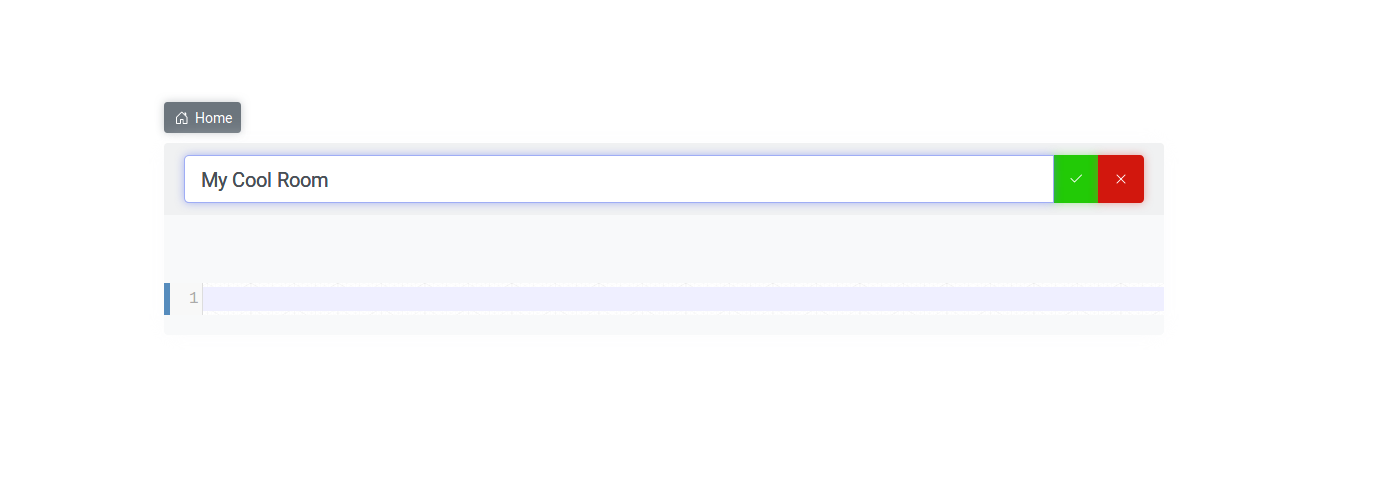
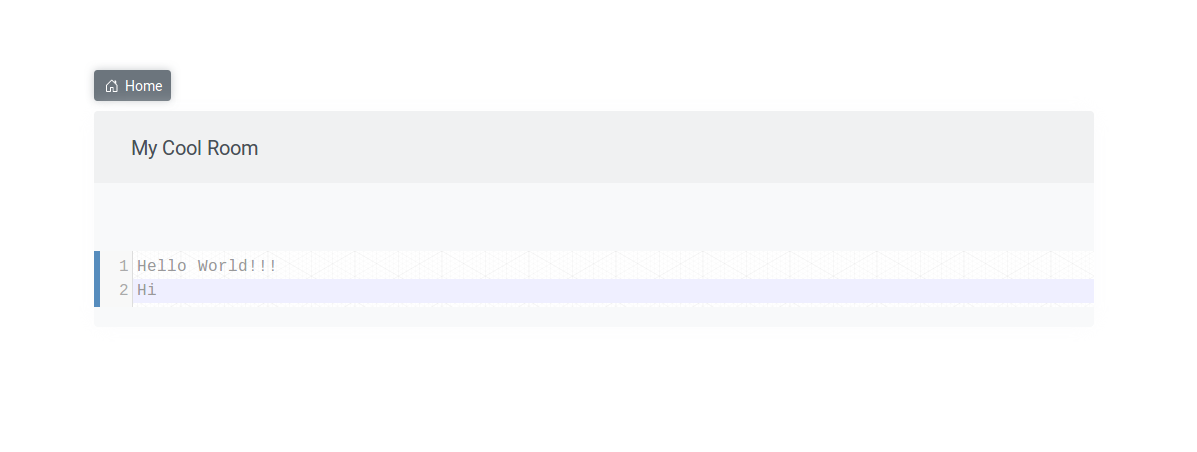
🔗py-matrix-utils
swedneck offered:
I'm working on a Gtk GUI for py-matrix-utils, progress can be followed at https://gitlab.com/Swedneck/py-matrix-utils This isn't going to be a fully fledged matrix client, it's just a graphical interface for various matrix tools.
🔗Dept of Ops 🛠
🔗matrix-docker-ansible-deploy Raspberry Pi support
Slavi offered:
Thanks to Gergely Horváth's efforts, matrix-docker-ansible-deploy now supports installing at least some of its services to a Raspberry Pi server.
See our Self-building documentation page to learn how to get started.
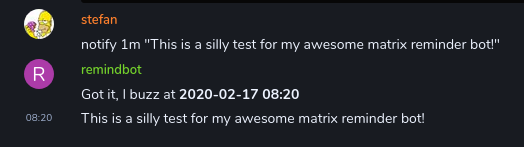
🔗Dept of Bots 🤖
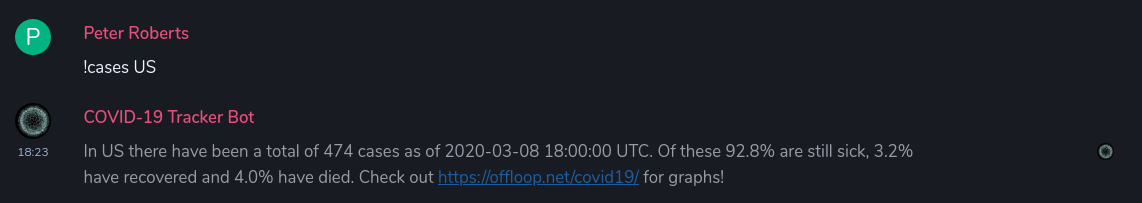
🔗CovBot v0.0.10
Peter Roberts announced:
- Search by country code.
- Better handling of issues in the data.
- Do more things with asyncio.
MIT licensed on GitHub.
Thanks to the super awesome bridging powers of Matrix anyone on WhatsApp can now chat with the bot! Feel free to chat with it and share with anyone who prefers to use WhatsApp!
More magic bridging means Telegram users can now chat with the bot! Please feel free to share with anyone who prefers to use Telegram!
Additionally:
CovBot has a couple of contributors working on it now too 🙂
Check the repo for details!
🔗Final Thoughts 💭
🔗Organising IT Support via Riot
Karl told us:
We are mid in building a team to give free IT support and security help to critical infrastructure operators during Corona times organized via Riot. Added a local alias for this room here at #helpeurope:matrix.org . room where we started creation #helpeurope:matrix.ctseuro.com. Everybody wanting to help is welcome.
Join the room and get involved for more info.
🔗Dept of Ping 🏓
Here we reveal, rank, and applaud the homeservers with the lowest ping, as measured by pingbot, a maubot that you can host on your own server. Join #ping:maunium.net to experience the fun live, and to find out how to add YOUR server to the game.
| Rank | Hostname | Median MS |
|---|---|---|
| 1 | maescool.be | 369 |
| 2 | imninja.net | 379.5 |
| 3 | envs.net | 380 |
| 4 | gottliebtfreitag.de | 382.5 |
| 5 | swag.industries | 423 |
| 6 | maunium.net | 449 |
| 7 | shortestpath.dev | 452 |
| 8 | lyseo.edu.ouka.fi | 454.5 |
| 9 | ilmari.org | 464 |
| 10 | nct08.de | 485 |
🔗That's all I know 🏁
See you next week, and be sure to stop by #twim:matrix.org with your updates!