This Week in Matrix 2022-01-21
2022-01-21 — This Week in Matrix — Thib🔗Matrix Live 🎙
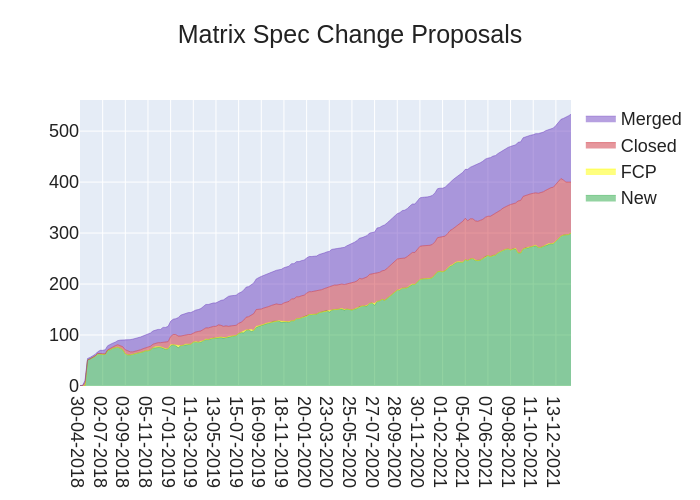
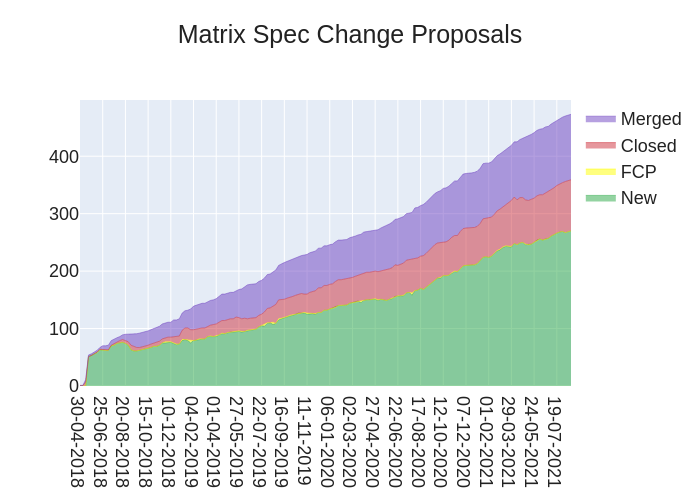
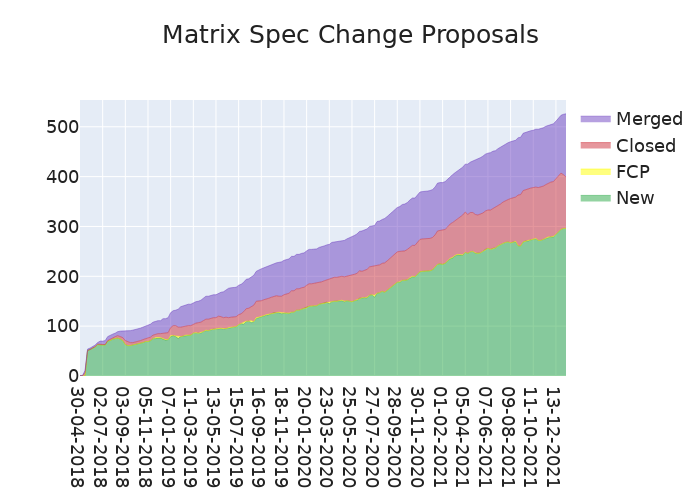
🔗Dept of Spec 📜
anoa reports
Here's your weekly spec update! The heart of Matrix is the specification - and this is modified by Matrix Spec Change (MSC) proposals. Learn more about how the process works at https://spec.matrix.org/unstable/proposals.
🔗MSC Status
New MSCs:
- MSC3664: Pushrules for relations
- [WIP] MSC3662: Allow Widgets to share user mxids to the client
- MSC3659: Invite Rules
- [WIP] MSC3647: Bring Your Own Bridge - Decentralising Bridges
MSCs with proposed Final Comment Period:
- MSC2781: Remove the reply fallbacks from the specification
- MSC3030: Jump to date API endpoint
- MSC3589: Room version 9 as the default room version
MSCs in Final Comment Period:
- No MSCs are in FCP.
Merged MSCs:
- MSC3567: Allow requesting events from the start/end of the room history
- MSC2675: Serverside aggregations of message relationships
🔗Spec Updates
Work on preparing the release of Matrix v1.2 is currently underway. As of today, the Spec Core Team is aiming for a release of Matrix v1.2 on February 2nd.
If you know of any MSCs which you believe should be included in Matrix v1.2, but haven't started/finished Final Comment Period yet, please bring them up in the #sct-office:matrix.org, and we'll take a look. Thanks!
🔗Random MSC of the Week
The random MSC of the week is... MSC3635: Early Media for VoIP!
When I first came across this MSC, I didn't know what "Early Media" as a concept referred to. Even after skimming the MSC... I still didn't really know. But I'll demystify it here in case it peaks your interest and you would like to learn more.
Early media is essentially any media that is exchanged between the moment you start a call, to the moment the other side picks up (a connection is established). For instance, the ringing you hear while waiting for someone to pick up (called "ringback tones"), or the "busy" tone you hear when the line is busy. Those audio bits are known as "early media". Video can also fall into this category (though that's less common).
This MSC would essentially allow Matrix to introduce these concepts in Matrix-only calls (though these days the client just plays sounds while connecting), but more crucially would allow Matrix to interoperate with other protocols (like SIP) that expect to handle these features.
So yay, more interoperability and bridge compatibility!
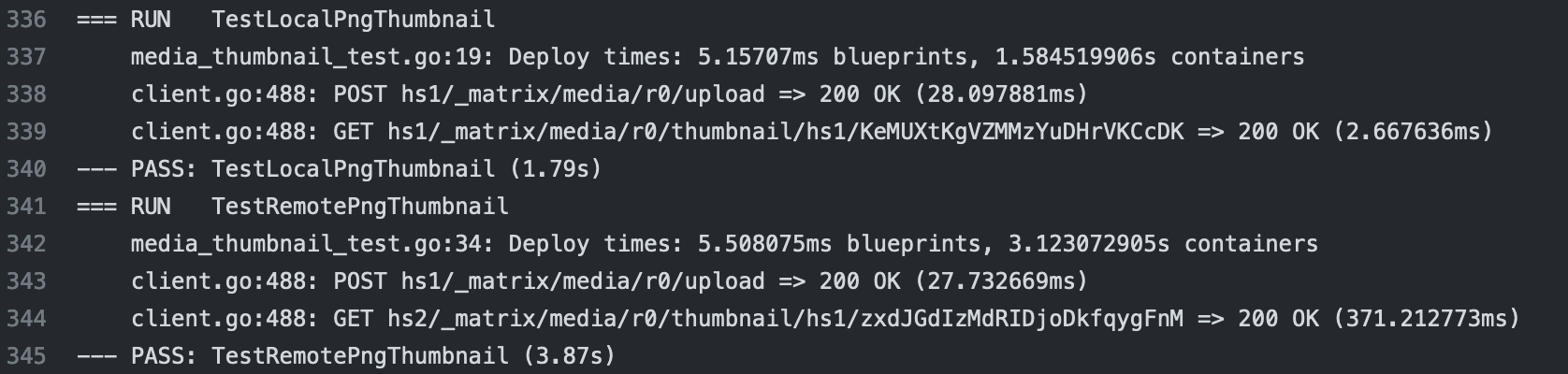
🔗Dept of Servers 🏢
🔗Synapse (website)
Synapse is the reference homeserver for Matrix
callahad says
After a somewhat bumpy process, we released Synapse 1.50 on Tuesday! The big thing you need to be aware of is that we're turning off support for Python 3.6 and PostgreSQL 9.6, including Linux distributions which ship with those versions by default (like Ubuntu 18.04 LTS). Please make sure your infrastructure is up-to-date.
I'm personally very excited that we tracked down a bug which could cause device list updates to get lost when being sent over federation. When device lists fall out of sync, it can cause failures when attempting to decrypt messages, since the keys may not have been sent to all of the user's devices.
We've also made quite a lot of progress in allowing Application Services to support end-to-end encryption via the still-experimental MSC3202.
For MSCs which have been merged into the Matrix Spec, we now implement MSC3419, allowing guests to send state events into rooms, and we now use stable identifiers for cross-signing and fallback keys per MSC1756 and MSC2732.
Looking to the future: We're aiming to release 1.51 next week so it has plenty of time to burn in before we host FOSDEM 2022. This is a pretty quick turnaround from 1.50, but we'll return to our usual fortnightly release cadence for subsequent releases. To that end, 1.51.0rc1 is out today; give it a shot. 😉
🔗Conduit (website)
Conduit is a simple, fast and reliable chat server powered by Matrix
Timo ⚡️ announces
Hello again! In the last week we continued to optimize the rocksdb backend and Conduit in general, trying to get it as memory efficient as possible. Using valgrind we could see that memory was not getting released in some cases.
We found out that switching to the
jemallocallocator completely got rid of this problem and memory usage seems to be a lot more stable now!All of this is currently available on the
nextbranch. We are preparing to make a v0.3.0 release soon!Join #conduit:fachschaften.org to help us test it.
Thanks to everyone who supports me on Liberapay or Bitcoin!
🔗Homeserver Deployment 📥️
🔗Helm Chart (website)
Matrix Kubernetes applications packaged into helm charts
Ananace announces
And back to regular form, my Helm Charts have gotten some upgrades again; element-web got upgraded to 1.9.9, and matrix-synapse got both 1.50.0 and 1.50.1 (the configuration generated by the chart shouldn't be affected by the .0 bug, but always good to upgrade)
🔗Dept of Clients 📱
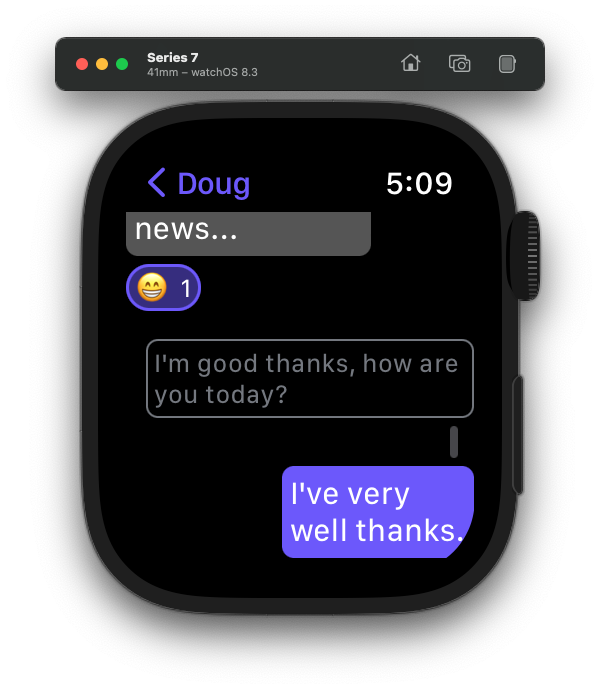
🔗Watch The Matrix (website)
A watchOS client for Matrix
Doug announces
It's been a while since I reported any updates on Watch The Matrix.
The following new features have been added:
- Message bubbles are properly left/right aligned now.
- Support for displaying images.
- Replies are nicely formatted now.
- Ability to send messages and replies (inc FlickType support).
- Redacted reactions are now properly hidden.
🔗Sailtrix (website)
Sailtrix is a matrix client for SailfishOS
HengYeDev announces
This week, version 1.3.7.1 has been released.
Updates:
- Support favorite rooms
- Add View Source
- Add useful active cover
- Merge better notification support by @razcampagne
Fixes:
- Fix bug of images and files not displaying in encrypted rooms
- Add UI placeholder when there are no rooms
🔗Element (website)
Everything related to Element but not strictly bound to a client
Danielle announces
Threads
- To keep your timeline clean and ordered we’ll soon be introducing threaded messages to Element. Currently the team is working hard on the fallback solution, and polishing up the user interface.
- Threads is already in Labs on Web, so go ahead and check it out!
- For mobile, we’re hoping to release Threads to Labs in the next few weeks.
Polls
- Get ready to start asking more questions… Polls are nearly ready to go! You’ll be able to ask folks things like; their favourite superhero, which day you should grab lunch, or even the best way to make tea (milk first, always). ☕️
- If you just can’t wait ‘til we’re ready to launch, you can enable Polls from Labs.
Location Sharing
- Location sharing is almost here! You’ll soon find a new setting to turn this on, which will give you the location sharing icon in your composer and can be used to tell people exactly where you are!
- The setting will be in the next release on iOS and Android, and will start “off” by default. Once the feature is settled in, we’ll turn it on by default.
Community testing
- Join #element-community-testing:matrix.org to help out with the testing
- We will be testing the FOSDEM conferencing setup (Element web + widgets) on Monday at 17:00 UTC
- Element Desktop (Nightly) has had an Electron update, join us to test it on Tuesday at 16:00 UTC
🔗Element Web/Desktop (website)
Secure and independent communication, connected via Matrix. Come talk with us in #element-web:matrix.org!
Danielle reports
- We’re moving forwards with our PostHog Analytics implementation and are super excited to start to get to know how our users experience Element. Remember; it’s off by default and you have to opt-in to share.
- 2 testing sessions happening this week, join at #element-community-testing:matrix.org
In labs (you can enable labs in settings on develop.element.io or on Nightly)
- With the coolest project name by far, the Bubbles team is working hard to bring you message bubbles ASAP! These should land in the next week or so but are available in Labs today.
🔗Element iOS (website)
Secure and independent communication for iOS, connected via Matrix. Come talk with us in #element-ios:matrix.org!
Danielle says
- The integration of analytics tracking has been included in the most recent version of the app. Using PostHog Analytics we’ll be able to make informed product decisions for our app as we’ll have more visibility into the usefulness of each feature.
- Remember; Analytics is opt-in and you don’t have to share any info with us. If you choose to opt-in we’ll start to learn how users use Element and how we can simplify your experiences.
In development:
- Work ongoing on Spaces support, finished improving room long press interactions for Spaces and reviews of space creation changes are nearing completion. Work ongoing on Space settings.
- We’re currently building a simplified first time user experience, the first piece of which will be released in the next few weeks!
- The team is working to update to Xcode 13 / iOS 15.
🔗Element Android (website)
Secure and independent communication for Android, connected via Matrix. Come talk with us in #element-android:matrix.org!
Danielle reports
- We’ve had some trouble with the stability of our releases this week but the team’s been working hard to get it all ironed out. Our latest update to the app store fixes some bugs and includes the option to enable analytics.
- Analytics? Yes! Knowing how our users traverse our app, and understanding this cross-platform, will help us to tailor to your needs and make impactful improvements. If you don’t want to send anonymised event info to Element, no problem! Just say no. If you change your mind, there’s a toggle in Settings.
In development:
- Message Bubbles? Yes, please! With a week of successful testing internally we’re nearly ready to release message bubbles into the wild. We’re excited to see what you think.
- Element’s first time user experience could use a little help, so the team have been working on improvements to our sign up flow that will hopefully reduce confusion for newbies.
🔗Dept of Non Chat Clients 🎛️
🔗Matrix Wrench (website)
Matrix Wrench is a web client to tweak Matrix rooms.
ChristianP says
New feature: HTTP status in the network log.
Next up: Bulk editing of rooms for updating room power levels or aliases in masses. If you're a maintainer of a homeserver, space or bridge, please let me know your use cases.
🔗export matrix messages (website)
A commandline utility to export matrix messages
Aine reports
It's a small cli tool that does exactly what it says - exports matrix messages from a room. As example you can check etke.cc/news - that page and all items on it generated by emm from #news:etke.cc room.
The tool gracefully supports room aliases, message edits, custom templates (check the
contrib/dir for example) and 2 export modes - single (all messages exported to a single file) or multi (each message exported to separate file, that's how etke.cc/news works)
🔗Circles (website)
E2E encrypted social networking built on Matrix. Safe, private sharing for your friends, family, and community.
cvwright announces
Circles is a project to build a privacy-respecting, end-to-end encrypted social network on top of Matrix. It was originally built out of the desire for a safer way to share baby photos with friends and family, but it can be used by anyone who wants easy sharing combined with strong security.
Recent news:
- The Circles iOS app is back in beta on TestFlight. Builds 0.99 (6) and 0.99 (8) are rolling out now.
- The latest updates fix some bugs in Circles' use of Matrix's encrypted recovery feature to improve the reliability of E2E encryption.
- FUTO, the new company behind Circles, is hiring an Android developer to help us bring Circles to Android. Interested candidates should send a resume and cover letter to [email protected].
The (old) Circles homepage: https://kombuchaprivacy.com/circles The code on Github: https://github.com/KombuchaPrivacy/circles-ios
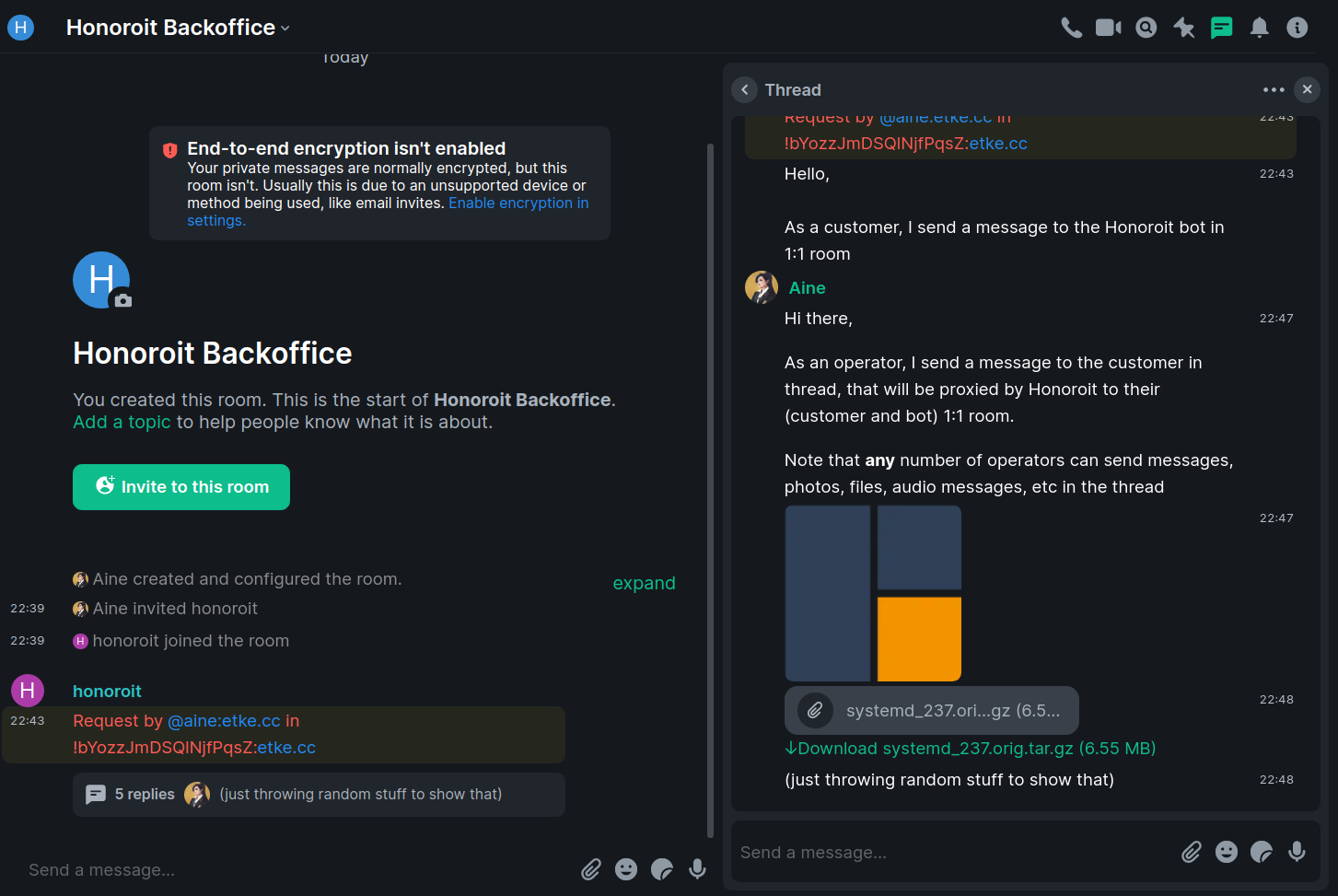
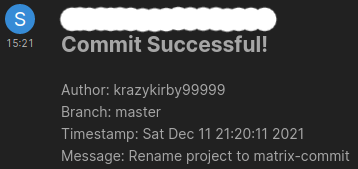
🔗Dept of Bots 🤖
🔗Honoroit (website)
A Matrix helpdesk bot
Aine reports
long time no see! Today I come with a new internal etke.cc tool that publicly available, because open source matters.
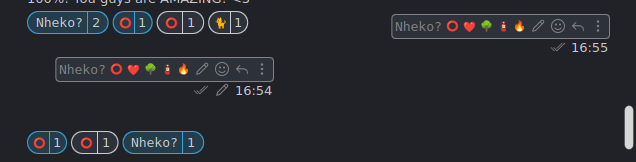
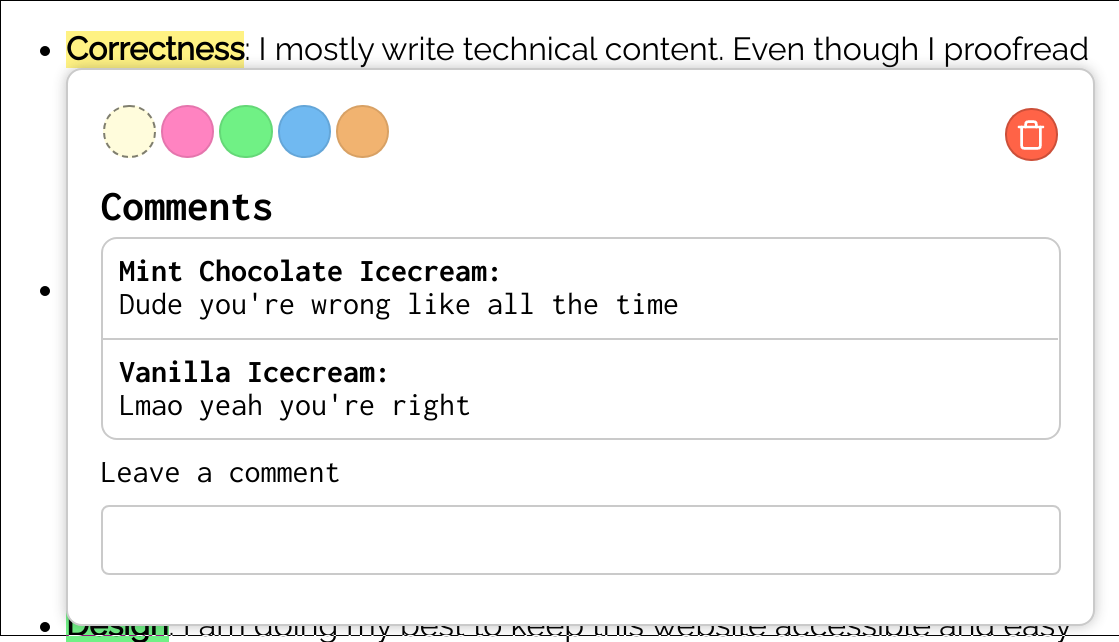
Honoroit is a helpdesk matrix bot with end-to-end encryption support, that utilizes MSC3440 (Threading) to act as a proxy between a customer (any matrix user) and your backoffice (users added in special room), each customer's room = thread in a backoffice room, where multiple operators can send messages to the same customer at once.
Pretty bad description, I know - check the source code to see screenshots.
Updates:
- the v0.9.2 release brings the fallback reply-to mode, so even on matrix clients that doesn't support threads yet you can use it with good ol' replies.
- the v0.9.3 release fixes commands parsing in the reply-to mode and adds prefixes to the thread topics
🔗Dept of Interesting Projects 🛰️
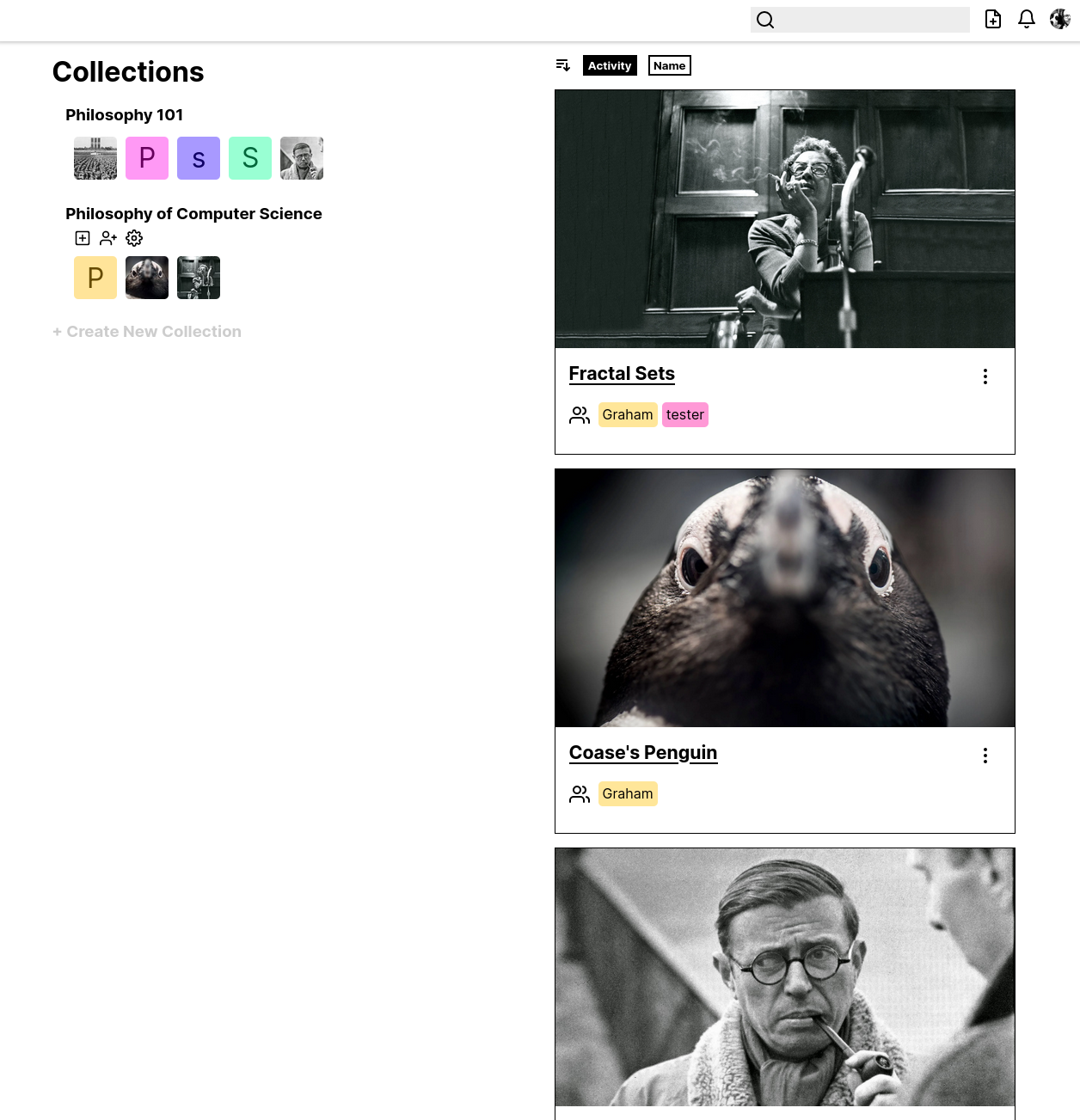
🔗matrix-art (website)
A Devianart Fork based on Matrix
MTRNord (they/them) says
Matrix Art received some minor changes since the last twim post:
- You can now get a rss feed of the posts at https://art.midnightthoughts.space/posts.rss (This is in the same format as devianart does their feeds)
- Mobile should be mostly fixed
- The About-info isn't hardcoded anymore but now uses an event type.
- The page now uses the Roboto Font instead of the default font, which helps with readability.
- Matrix Art cmes with a basic Text Logo now
- Links to the profile page are now easier to notice
- Blurhashes are now supported for images
- The repo now has the Apache-2 License applied
- Dependencies have been pinned
- Various small design improvements were made
- Images now have size hints so the page doesnt jump around as much when loading
- Lots and lots of metadata was added to each page for SEO
Check it out at https://art.midnightthoughts.space Check the Code out at https://github.com/MTRNord/matrix-art Or join the Chat at #matrix-art:nordgedanken.dev
Planned for this week is to add registration and usage of external profiles. As soon as that works I am also going to make uploading images work. So with a bit of luck in the next TWIM anyone is able to post their images :)
🔗Dept of Guides 🧭
Éibhear (on matrix.org) reports
Hi TWIM. I published a long-planned, long-in-the-making, long-winded report of how I containerised my matrix-synapse homeserver and its PostgreSQL database in order to get ahead of the application dependency deprecations. This was something I couldn't find for myself, so I put this together to help anyone else who might need it. (And it does contain a TL;DR section!)
Helder Ferreira says
I’ve created blog post explaining the way to host the static well-known files using cloudflare workers gaining speed and stability
🔗Matrix in the News 📰
Brendan Abolivier says
During the holidays I recorded a podcast about Matrix and Element with AnDaolVras/La Cantine Brestoise, which is a French non-profit organising tech events and operating a coworking space in Brest, France. The episode (in French, sorry!) came out on Monday and can be found on their website, on YouTube as well as on most podcast platforms 🙂
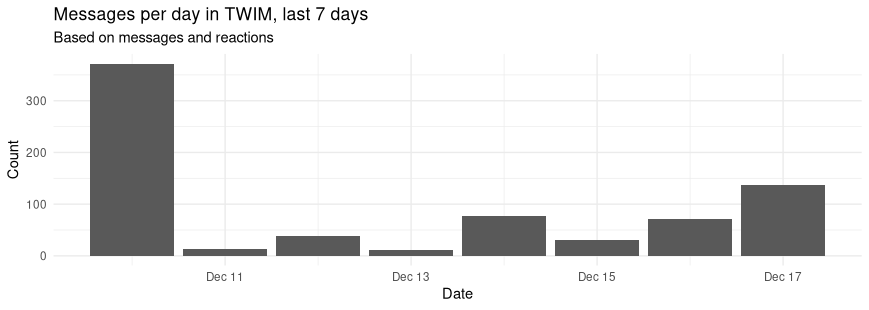
🔗Dept of Ping 🏓
Here we reveal, rank, and applaud the homeservers with the lowest ping, as measured by pingbot, a maubot that you can host on your own server.
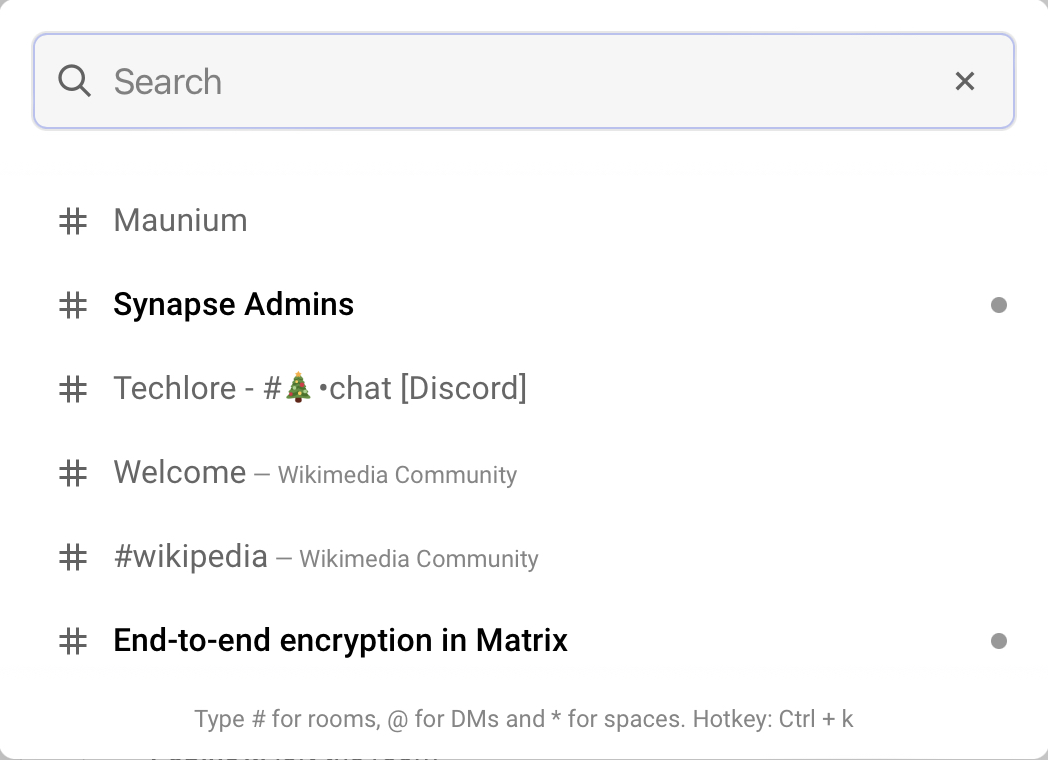
🔗#ping:maunium.net
Join #ping:maunium.net to experience the fun live, and to find out how to add YOUR server to the game.
| Rank | Hostname | Median MS |
|---|---|---|
| 1 | envs.net | 517 |
| 2 | talkthings.net | 687 |
| 3 | aria-net.org | 821 |
| 4 | reactos.org | 869 |
| 5 | matrix.xn--kll-sna.net | 1109 |
| 6 | trygve.me | 1881 |
| 7 | minecraftchest1-matrix.loca.lt | 1922.5 |
| 8 | matx.myecloud.org | 2453 |
| 9 | thomcat.rocks | 2949 |
| 10 | asra.gr | 3546.5 |
🔗#ping-no-synapse:maunium.net
Join #ping-no-synapse:maunium.net to experience the fun live, and to find out how to add YOUR server to the game.
| Rank | Hostname | Median MS |
|---|---|---|
| 1 | sspaeth.de | 367 |
| 2 | dendrite.matrix.org | 423 |
| 3 | rustybever.be | 606 |
| 4 | conduit.rs | 908.5 |
| 5 | dendrite.neilalexander.dev | 926 |
| 6 | matrix.awesomesheep48.me | 1160.5 |
| 7 | dendrite.beckmeyer.us | 1856 |
| 8 | conduit.cyberdi.sk | 3547 |
🔗That's all I know 🏁
See you next week, and be sure to stop by #twim:matrix.org with your updates!