The original promise of the Internet was to be an interoperable platform for distributing data. However, we have since increasingly seen our data fragmented and trapped in a number of proprietary silos. Matrix hopes to fix this by being a federated, open standard for data exchange that any service can use.
The Decentralized Web Summit is a meetup for anyone interested in building the Decentralized Web, which aims to make the Web open, secure and free of censorship by distributing data, processing, and hosting across millions of computers around the world, with no centralized control. It takes place at the Internet Archive, San Francisco, CA on Wednesday June 8 and Thursday June 9, 2016.
Matrix will be represented at the event, and we hope to also host a workshop or a talk about Matrix.
The meetup has a Slack room set up for pre-meetup conversations - you can also access this room via Matrix: #decentralizedweb-general:matrix.org
We are looking forward to interesting people and interesting conversations at the first Decentralized Web Summit!

Last week I went to Kamailio World 2016 in Berlin to meet fellow VoIP-developers and tell them all about Matrix. It's a fairly small conference, which is actually quite nice as it means you get to talk to almost everyone. A lot of people were interested in Matrix - both new and familiar faces - in fact, some of them heard about Matrix a year ago at Kamailio World 2015 and were interested in hearing what progress we've made since.
As always, Matrix participated in James Body's dangerous demos session - and I also gave a 30min talk on Matrix and recent updates to a full room on the first day of the conference.
Several people mentioned that Matrix could be interesting to their project, either as a glue between services, or for adding text-based chat to VoIP apps. I hope to see some of you in Matrix at some point - please join us in #matrix:matrix.org and say hi! It's also a good place to ask questions and discuss how Matrix can work with your project. Auf Wiedersehen!
Congratulations to Aviral Dasgupta and Will "Half-Shot" Hunt who will be working with Matrix for their Google Summer of Code projects!
As mentioned, picking two projects out of all our proposals was no easy task. However, we now look forward to getting started, and we are sure Aviral and Half-Shot will help make Matrix even better over the next few months!
Aviral will be developing a flexible plugin system to facilitate integrating various services such as github/trello/duckduckgo with Matrix. Meanwhile, Half-Shot will be looking at adding features on top of Matrix - infact, he's already built a MPD DJ bot and started working on a .NET SDK. Aviral too, has been committing various enhancements already.
According to Google's GSoC timeline we are currently in the "Community Bonding" phase, which lasts till May 22, 2016 - which is when the projects formally kick off.
We're looking forward to seeing what awesome things Aviral and Half-Shot come up with!
As previously announced, Matrix is participating in Google Summer of Code (GSoC) 2016. We have had a lot of interest: lots of people joining Matrix to talk to us about their project ideas and a total of 38 project proposals. We have even had some code contributions to our various projects from people who discovered Matrix via GSoC!
It's our first year as a GSoC mentoring organisation and we were only allocated two project slots. This means that we had the tough decision of choosing between some really good projects - and that means a lot of you who applied will unfortunately be left feeling disappointed. Selecting our two projects was very difficult, and we talked it over until we all agreed. Please remember that not being picked does not mean that your proposal was bad.
If you missed out on a GSoC slot this year, that doesn't have to stop you from contributing, either by hacking on your own project or contributing to an existing Matrix project. It's a great way to hone your programming skills and we'll be more than happy to help out and support you - find us in #matrix:matrix.org and #matrix-dev:matrix.org.
All the best from the Matrix team and good luck to everyone in their summer projects, whether GSoC or not!
TADHack-mini took place in east London over the weekend with 88 people in attendance. There were $8k in prizes, and five different services to hack on. This time, we didn't have too many people using Matrix in their hack, but we did have an excellent idea and implementation called Babelonio, who won our prize: a Phantom X Hexapod Mk3!
Babelonio adds speech-to-text and translation via Google translate to Matrix, via the Vector client and a Chrome extension. This is quite nice, because it means you don't have to run a custom client. And by using Google translate, you immediately get access to a lot of languages (although sometimes the translation doesn't quite work, as you can see in the presentation video). The project was done by Steven Bakker, Timo Uelen and Bart Uelen. You can see the presentation and demo of the hack here.
A good write-up of all the hacks and winners can be found on the TADHack blog.
Thanks to the TADHack organisers for another fine event, and also to everyone who came over to chat about Matrix - and again congratulations to the Babelonio team:


It's soon time for the 2nd TADHack-mini London. The event starts at 10am on Saturday April 9th and hacking continues until the projects are pitched, starting at 1pm on Sunday April 10th. As you can see by the many previous TADHacks, every hackathon brings interesting and impressive projects, so we are again expecting great things!
As usual, there are great prizes to be won - worth around $5k in total. This time, we will award the best Matrix-related hack a PhantomX AX Metal Hexapod Mark III from Trossen Robotics, a build-it-yourself hexapod robot kit! The robot is built on an entirely open source platform, complete with 3D cad models of the robot, open software, and schematics for the electronics.

If you're planning to attend TADHack-mini London: see you there! If not - why aren't you? Consider spending a day and a half hacking on some cool technologies - it could be well worth your time!
You can be one step ahead by getting acquainted with the Matrix C-S API or the AS API. And if you have any questions - or want to discuss potential hacks - please come talk to us in #matrix:matrix.org!
We just released Synapse 0.14.0 - a major update which incorporates lots of work on making Synapse more RAM efficient. There's still a lot of room for further improvements, but the main headlines are reducing the resident memory footprint dramatically by interning strings and deduplicating events across the many different caches. It also adds a much-needed SYNAPSE_CACHE_FACTOR environment variable that can be used to globally decrease or increase the sizing of all of Synapse's various caches (with an associated slow-down or speed-up in performance). Quite how improved the new memory footprint seems to very much depend on your own use case, but it's certainly a step in the right direction.
For more details on recent Synapse performance work (and a general state of the union for the whole Matrix ecosystem), check out our Spring update.
Get all new synapse from https://github.com/matrix-org/synapse - we recommend upgrading (or installing!) asap :)
Full changelog follows:
🔗Changes in synapse v0.14.0 (2016-03-30)
No changes from v0.14.0-rc2
🔗Changes in synapse v0.14.0-rc2 (2016-03-23)
Features:
- Add published room list API (PR #657)
Changes:
- Change various caches to consume less memory (PR #656, #658, #660, #662, #663, #665)
- Allow rooms to be published without requiring an alias (PR #664)
- Intern common strings in caches to reduce memory footprint (#666)
Bug fixes:
- Fix reject invites over federation (PR #646)
- Fix bug where registration was not idempotent (PR #649)
- Update aliases event after deleting aliases (PR #652)
- Fix unread notification count, which was sometimes wrong (PR #661)
🔗Changes in synapse v0.14.0-rc1 (2016-03-14)
Features:
- Add event_id to response to state event PUT (PR #581)
- Allow guest users access to messages in rooms they have joined (PR #587)
- Add config for what state is included in a room invite (PR #598)
- Send the inviter's member event in room invite state (PR #607)
- Add error codes for malformed/bad JSON in /login (PR #608)
- Add support for changing the actions for default rules (PR #609)
- Add environment variable SYNAPSE_CACHE_FACTOR, default it to 0.1 (PR #612)
- Add ability for alias creators to delete aliases (PR #614)
- Add profile information to invites (PR #624)
Changes:
- Enforce user_id exclusivity for AS registrations (PR #572)
- Make adding push rules idempotent (PR #587)
- Improve presence performance (PR #582, #586)
- Change presence semantics for
last_active_ago (PR #582, #586)
- Don't allow
m.room.create to be changed (PR #596)
- Add 800x600 to default list of valid thumbnail sizes (PR #616)
- Always include kicks and bans in full /sync (PR #625)
- Send history visibility on boundary changes (PR #626)
- Register endpoint now returns a refresh_token (PR #637)
Bug fixes:
- Fix bug where we returned incorrect state in /sync (PR #573)
- Always return a JSON object from push rule API (PR #606)
- Fix bug where registering without a user id sometimes failed (PR #610)
- Report size of ExpiringCache in cache size metrics (PR #611)
- Fix rejection of invites to empty rooms (PR #615)
- Fix usage of
bcrypt to not use checkpw (PR #619)
- Pin
pysaml2 dependency (PR #634)
- Fix bug in
/sync where timeline order was incorrect for backfilled events (PR #635)
It's been 3 months since the Matrix Holiday Special and once again we've all been too busy writing code to put anything that detailed on the blog. So without further a do here's a quick overview of how things have progressed so far in 2016!
🔗Home servers
🔗Synapse
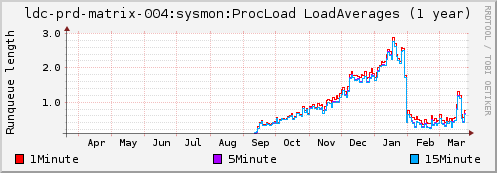
Work on Synapse (our reference homeserver) has been primarily focused on improving performance. This may sound boring, but there's been a huge amount of improvement here since synapse 0.12 was released on Jan 4. Synapse 0.13 on Feb 10 brought huge CPU savings thanks to a whole fleet of caching and other optimisation work - the best way of seeing the difference here is to look at the load graph of the server that hosts matrix.org's synapse+postgres over the last few months:
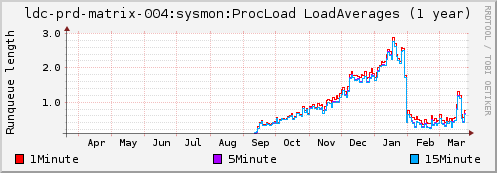
Ignoring the unrelated blip during March, you can see an enormous step change in system load (which had a matching decrease in actual CPU usage) at the beginning of Feb when the 0.13 optimisations landed on matrix.org :)
Continue reading…

We are very happy to be one of the companies selected for Google Summer of Code (GSoC) 2016!
GSoC is a great, global opportunity for students to work on open source projects during their university summer break. The idea is for students to propose a project for any of the open source organisations picked by Google, and - if accepted - receive a stipend for working on it. We are very eager to see what projects students will propose - we have written up some ideas here, but students are expected to do some research and come up with projects themselves.
If you are a student wanting to participate in GSoC for Matrix, please come talk to us in #gsoc:matrix.org - we are happy to discuss project ideas and review application drafts. We have also added some general tips on what to include in the application here.
Applications can be submitted starting next Monday, so there's still plenty of time to have a play with Matrix and come up with a cool project idea.
Good luck!
The try-matrix-now page is now being generated by jekyll and all the project pages have been moved to the matrix-doc project on github.
The idea is to make it very easy for anyone to add or update a project entry. All you need to do is to submit a PR with the project details; feel free to start with the template, and you can also add images (thumbnail and/or a main picture for the project page) to the images subfolder (just use the same relative URL that is in the template). Any kind of project using Matrix is welcome; if you are unsure which category to use, just use "other".
Jekyll requires a date in the project filename; we use the date to sort the various project lists (newest projects first). It might be best to submit new entries with a date like 2015-01-01.
Any questions or comments? Come talk to us in #matrix:matrix.org!