This Week in Matrix 2022-08-26
2022-08-26 — This Week in Matrix — Brendan AbolivierLast update: 2022-08-26 18:43
Happy TWIMday everyone! Thib is away this week again, so I'm covering for him as your host in this edition of This Week In Matrix.
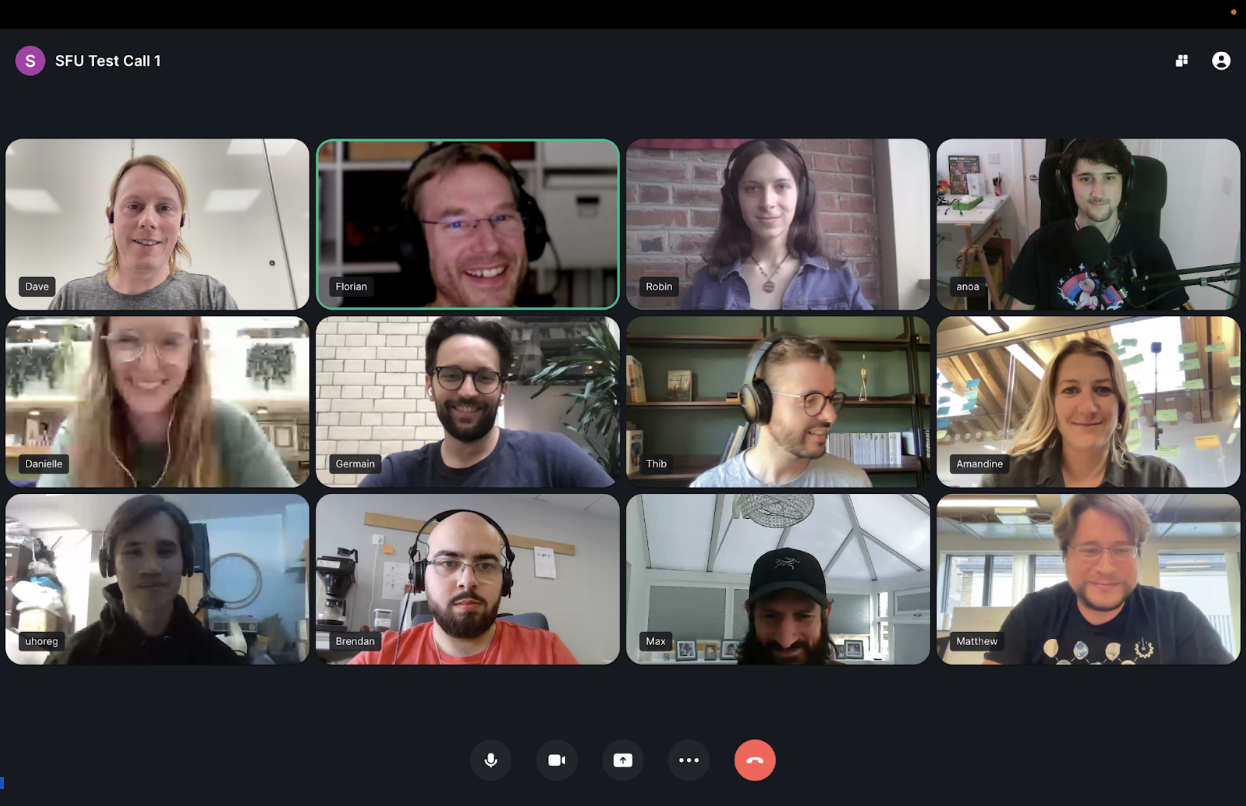
🔗Matrix Live 🎙
Following up on last week's tutorial about using Docker Compose to install Synapse, this week Thib explains how to use Ansible to deploy your own Matrix homeserver.
🔗Dept of Status of Matrix 🌡️
TravisR reports
Earlier in the year, t2bot.io passed 1 Million known rooms and now it's passed 10 Million bridged users (10,039,915 users to be exact, at time of writing). Most of these users will be people who have participated in a channel/chat on Discord or Telegram that was bridged to Matrix through t2bot.io's free service, with about 500 thousand being active each month.
Approximately 8 Million of the users are from Telegram, covering about 11% of all Telegram users (previously 15% based on information available at the time). The remaining 2 Million are Discord users, roughly 0.5% of Discord's user base. For perspective, t2bot.io has just over 683 Million events in the database and is bridging between 30 and 40 thousand people a day.
Like last time, this is just a milestone update, though it's also a good reminder to host your own server if you can. Element's own hosting platform is a great option if you'd like to have a server without running it yourself, and Beeper offers a richer bridging experience than t2bot.io can feasibly provide. If you'd like to go down the self-hosting route, check out Thib's video guide on hosting synapse or last week's Matrix Live for a better understanding of what hosting Synapse actually means.
As for an interesting statistic: despite not having much functionality that deals with Spaces, t2bot.io can see 2687 Spaces from the wider world. The plan in the coming months is to support a way to bridge a whole Discord server to a Matrix Space, making this statistic hopefully more interesting as time goes on.
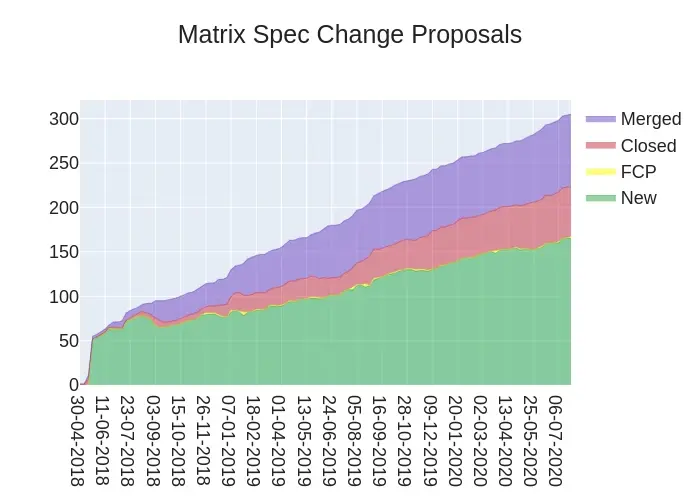
🔗Dept of Spec 📜
uhoreg reports
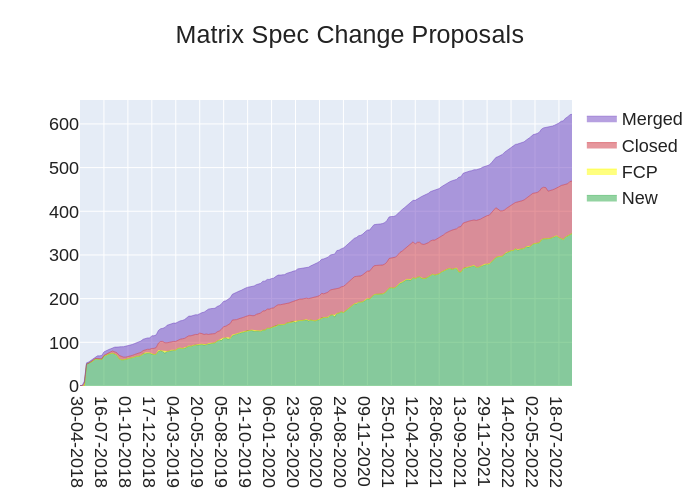
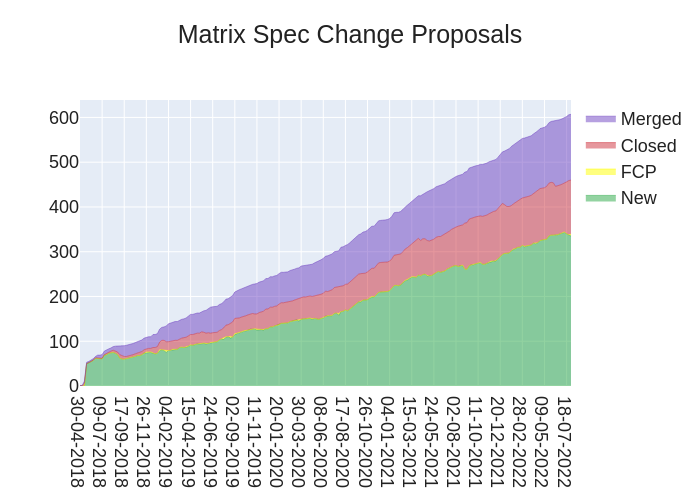
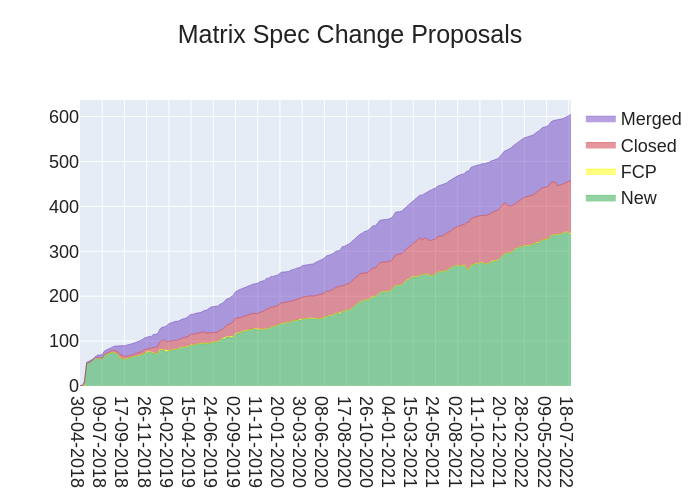
Here's your weekly spec update! The heart of Matrix is the specification - and this is modified by Matrix Spec Change (MSC) proposals. Learn more about how the process works at https://matrix.org/docs/spec/proposals.
🔗MSC Status
Merged MSCs:
- No MSCs were merged this week.
MSCs in Final Comment Period:
- No MSCs are in FCP.
New MSCs:
- MSC3874: Filtering threads from the /messages endpoint
- MSC3873: event_match dotted keys
- MSC3872: Order of rooms in Spaces
🔗Spec Core Team
The Spec Core Team has been continuing to push forward on the spec. Several new MSCs have been opened recently. The Spec Core Team is available in #sct-office:matrix.org when MSC authors think that they are ready for primetime.
🔗Random MSC of the Week
The random MSC of the week is... MSC2162: Signaling Errors at Bridges!
Bridges sometimes are unable to relay messages to the remote service for one reason or another. This MSC proposes a way to allow bridges to indicate that a message failed to be delivered, and allow users to tell the bridge to retry.
🔗Dept of Outreachy 🎓️
andybalaam announces
Usman's internship, working on Favourite Messages, is coming to an end! Check out Usman's blog post and Andy's blog post! To follow progress on Favourite Messages (which is still very much a prototype), check out the tracking issue: Tracking issue for Favourite Messages. Thanks to Usman for being an awesome mentee!
🔗Dept of Servers 🏢
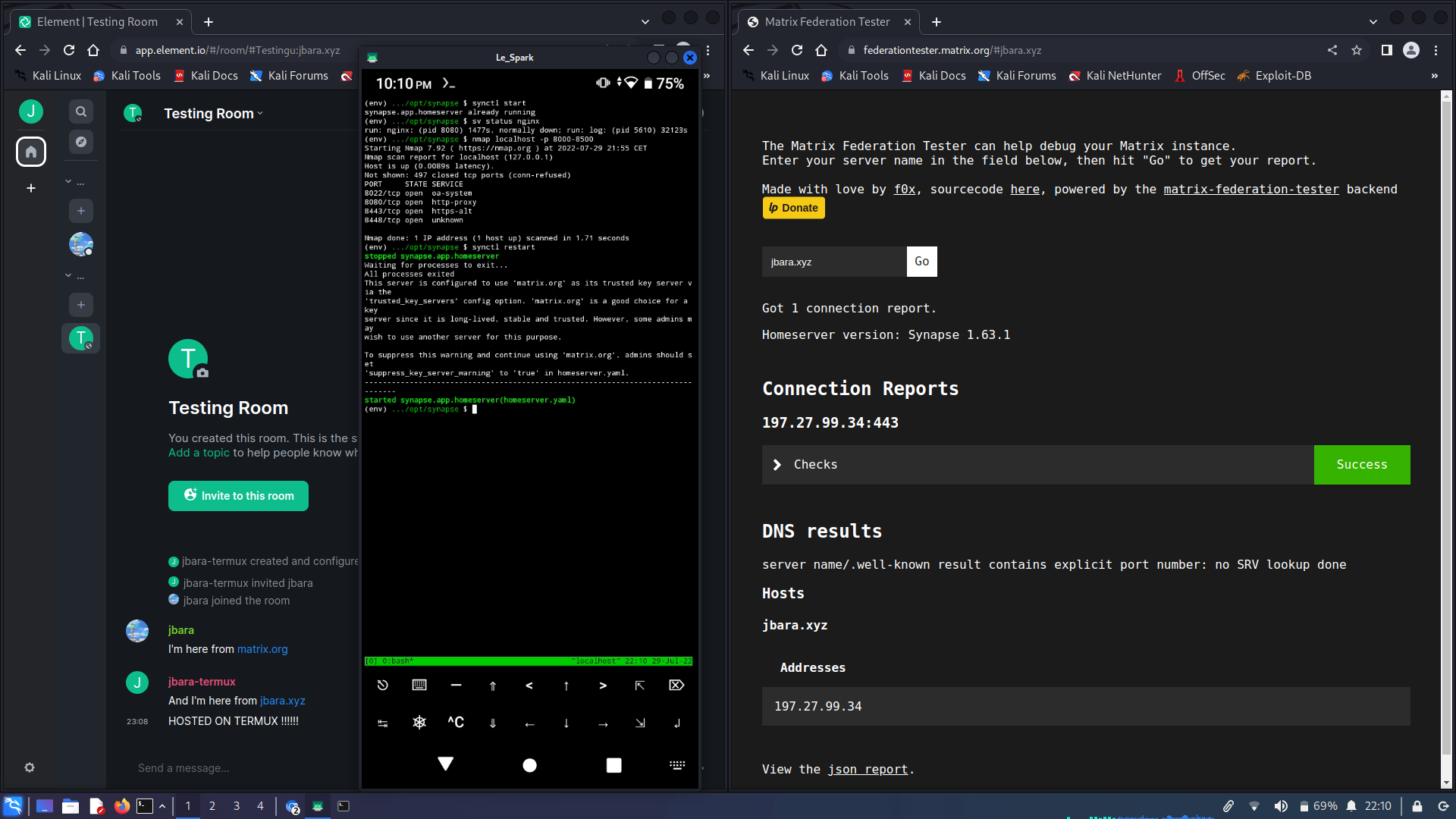
🔗Synapse (website)
Synapse is a Matrix homeserver implementation developed by the matrix.org core team
Brendan Abolivier says
This week we've released Synapse 1.66.0rc1! This upcoming release deprecates delegating email validation to an identity server (more info here) and includes improved validation around user-interactive authentication, support for a couple of experimental features, as well as the usual batch of bug fixes and performance improvements 🙂
As always, any help with testing and feedback on this RC is appreciated! Feel free to drop any feedback or bug report in #synapse:matrix.org and the Synapse repo respectively.
🔗Dendrite (website)
Second generation Matrix homeserver
neilalexander announces
This week we released Dendrite 0.9.5 which includes a number of fixes, particularly for federation:
- The roomserver will now correctly unreject previously rejected events if necessary when reprocessing
- The handling of event soft-failure has been improved on the roomserver input by no longer applying rejection rules and still calculating state before the event if possible
- The federation
/stateand/state_idsendpoints should now return the correct error code when the state isn't known instead of returning a HTTP 500- The federation
/eventshould now return outlier events correctly instead of returning a HTTP 500- A bug in the federation backoff allowing zero intervals has been corrected
- The
create-accountutility will no longer error if the homeserver URL ends in a trailing slash- A regression in
/syncintroduced in 0.9.4 should be fixedAs always, please feel free to join us in #dendrite:matrix.org for more Dendrite-related discussion.
🔗Dept of Ops 🛠
🔗matrix-docker-ansible-deploy (website)
Matrix server setup using Ansible and Docker
Slavi reports
Thanks to Aine of etke.cc, matrix-docker-ansible-deploy can now set up the new Postmoogle email bridge/bot. Postmoogle is like the email2matrix bridge (also already supported by the playbook), but more capable and with the intention to soon support sending emails, not just receiving.
See our Setting up Postmoogle email bridging documentation to get started.
🔗Dept of Bridges 🌉
Aine reports
follow-up to Slavi's announcement: Postmoogle is here!
Actually, he explained it pretty good, so here are some additional links
Source code and Roadmap with implemented and planned features and as usual, say hi in the #postmoogle:etke.cc
🔗Dept of Clients 📱
🔗Quadrix (website)
A Minimal, simple, multi-platform chat client for the Matrix protocol.
JFA says
Quadrix v1.2.5 has been released! The update is already available for Linux, MacOS and iOS. The Windows and Android updates are awaiting approval from the respective stores. This release has mostly "under the hood" improvements (upgrade to React Native 0.69, React 18 and other key dependencies), but also fixes a few bugs and brings minor UI improvements.
Great news: Quadrix finally made it to https://matrix.org/clients/ :-) Many thanks to @madlittlemods:matrix.org!!!
Please leave feedback/comments at #quadrix:matrix.org or in the issues at https://github.com/alariej/quadrix (stars welcome :-))
🔗Element Web/Desktop (website)
Secure and independent communication, connected via Matrix. Come talk with us in #element-web:matrix.org!
kittykat says
- Our code style guide has now finished review and we are now working on updating eslint-plugin-matrix-org to match it
- We will be release an RC2 to fix a regression around progress bars
In labs (you can enable labs features in settings on develop.element.io or on Nightly):
- We’re working hard on updating Threads, squashing bugs and improving performance. We have several MSCs open introducing new functionality to read receipts so that notifications work better than ever.
🔗Element iOS (website)
Secure and independent communication for iOS, connected via Matrix. Come talk with us in #element-ios:matrix.org!
Ștefan reports
- We’re working hard on making the new layout ready for general use, squashing bugs and taking names until everything is in tip top shape. We have a test flight build out: we’ve delayed the release to next week while we iron out the last creases.
- In ElementX land we have started on adding analytics and Xcode Cloud support and have updated our logging strategy. We will also start adopting sliding sync and using the new Rust Timeline providers
🔗Dept of VoIP 🤙
🔗Element Call (website)
Native Decentralised End-to-end Encrypted Group Calls in Matrix, as a standalone web app
Robin announces
Element Call v0.2.7 and v0.2.8 have been released this past week, adding local volume control, full screen mode, audio in screen sharing and, ahem, fixing an embarrassing bug where we broke walkie-talkie mode... 🐑 Oh, and it's also all in TypeScript now. 🚀 https://github.com/vector-im/element-call/releases/tag/v0.2.7
🔗Dept of SDKs and Frameworks 🧰
🔗simplematrixbotlib (website)
simplematrixbotlib is an easy to use bot library for the Matrix ecosystem written in Python and based on matrix-nio.
HarHarLinks says
simplematrixbotlib has reached version 2.7.0, adding support for end-to-end encryption! 🎉 Come chat over at #simplematrixbotlib:matrix.org!
Here is a summary of things that have happened since we last announced v2.6.3 on this channel:
- 🌐 The repo canonically moved to https://github.com/i10b/simplematrixbotlib, but the PyPI package remains available in the usual place.
- 🔒️ E2EE support! To enable it, simply install the optional e2ee dependencies. Find out how in the manual.
- 😄 Emoji verification support! Enable the option and you'll be able to interactively verify between the bot and your devices. (But mind that for now, in-room verification is not supported, but only to-device).
- ☝️ Fingerprint verification support! As an additional method, the bot will print it's encryption fingerprint so you can "manually verify".
- 🗄️ Extensible config file! It is now easier than ever to add your own configuration options to the built-in TOML config file.
- 🧹 The usual housekeeping, bumping matrix-nio to 0.19.0.
- 🗨️ I (HarHarLinks) will be presenting the library this weekend at #matrix-summit-berlin-2022:c-base.org! If you are in the Berlin 🇩🇪 area, come visit c-base!
The easiest to use bot library for Matrix. Get started in just 10 lines of code:
import simplematrixbotlib as botlib config = botlib.Config() config.emoji_verify = True creds = botlib.Creds("https://home.server", "user", "pass") bot = botlib.Bot(creds, config) @bot.listener.on_message_event async def echo(room, message): if botlib.MessageMatch(room, message, bot, PREFIX).is_not_from_this_bot(): await bot.api.send_text_message(room.room_id, message.body) bot.run()
🔗matrix-rust-sdk (website)
Matrix Client-Server SDK for Rust
ben announces
With a few people out of office, this weeks has been one of the more quiet ones, but progress has been made non-the-less. Again a lot happens in draft PRs and the background, like with the upcoming Timeline API but also the path forward for integrating the crypto bindings into the js-sdk. There are a few notable PRs merged this week still improving the API (#972 and #973, #961), upgrading to latest ruma, removing dependencies (
parking_lot) to improve compile times as well as merging the release infrastructure for crypto-js.👉 Wanna hack on matrix rust? Go check out our
help wantedtagged issues and join our matrix channel at Matrix Rust SDK.
🔗Dept of Bots 🤖
🔗Alertbot (website)
moanos [he/him] announces
This new bot allows users to use webhooks to forward monitoring alerts (e.g from prometheus) to matrix rooms. This means that you no longer have to use E-Mail or Slack to receive alerts. To set it up visit Github Alertmanager or join #alertbot:hyteck.de
🔗Opsdroid (website)
An open source chat-ops bot framework
Oleg says
Though this release doesn't include Matrix-related changes. Still there are new feature and fixes worth mentioning:
- The brand new command center backend (docs) from @FabioRosado
- Several fixes to the Slack connector contributed by @chillipeper
- A fix to the Telegram connector from @D3N14L
- Couple of fixes to the Websocket connector from @FabioRosado
- And a lot of fixed links in the docs by @jaas666
- Also now the
devDocker image tag (ghcr, Docker Hub) is built on every commit to main/master branchThanks for all the contributions! 🙌 See the full changelog for details.
🔗Dept of Events and Talks 🗣️
HarHarLinks says
Greetings to the world from #matrix-summit-berlin-2022:c-base.org!
🔗Dept of Interesting Projects 🛰️
Array in a Matrix reports
Matrix AI that generates messages based off other users' messages using a neural network. The bot trains its GPT-2 model using the CPU and is written in JavaScript (Node.JS) and Python. The project's code can be found here.
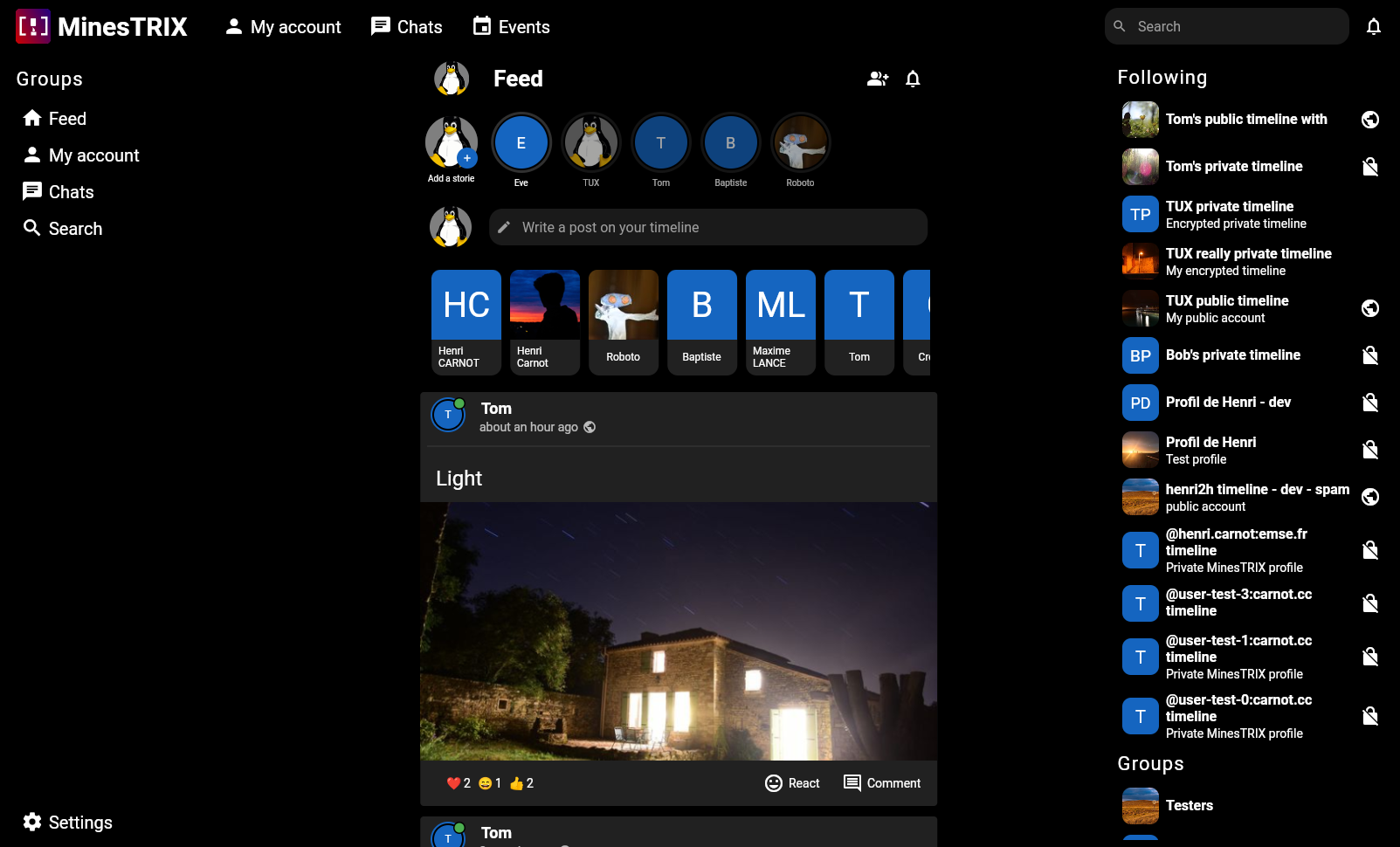
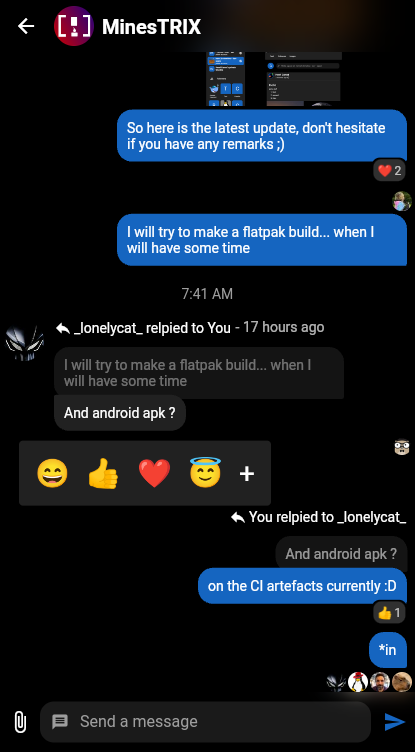
🔗MinesTRIX (website)
A privacy focused social media based on MATRIX
Henri Carnot reports
Hi all, quite a lot happened since the last twim post a few months ago.
In a nutshell, we refactored the feed page and user page for a better viewing experience. We also now allow displaying and commenting post images in a dedicated view. Also, you can now send follow request using knocking, thanks to profile as space support. (Yes, MSC is coming)
Finally, we have now multi account support, better stories display and refactored login and settings page.
Well... we almost modified everything :D
See more at https://minestrix.henri2h.fr/posts/
Stay tuned, event organization is coming soon (you can see the first implementation in the blog post.
PS: For those at the Matrix summit, I will be presenting it tomorrow
🔗Dept of Guides 🧭
Nate Covington reports
I recently made a blog post / video walk through of Matrix, hopefully it will be helpful to someone: https://www.covingtoncreations.com/blog/what-can-matrix-do-for-your-organization
🔗Room of the Week 📆
ssorbom ⚡️ says
Have you ever felt lost in the Matrix world? Too many rooms and spaces to manage? Well, back by popular demand (with Timo's blessing), I present, The Room of the Week! Every week we strive to highlight a room or a space that we believe deserves attention for discussing interesting going on across the Matrix Network.
This week on room of the week:
We Are All Tech enthusiasts on The Matrix Network, but do you ever experience Tech burnout? Do you ever wish you could find discussions in The Matrix Universe about things other than Tech? Well, this week we bring you a very technical solution!
Because we are highlighting:
A space where you will find information about everything except technology. Groups are helpfully categorized by Subspace, and feature discussions about everything from musical instruments to beverages. If it isn't about computing, it's there.
If you have a room you wish to see highlighted, join us at: https://matrix.to/#/!bIyiUUnriVoHtYzuPS:fachschaften.org?via=chat.shawnsorbom.net&via=matrix.org&via=fachschaften.org To get your favorite room of the week highlighted.
🔗Dept of Ping 🏓
No ping stats while Thib is away, but you can always join the fun at #ping:maunium.net and #ping-no-synapse:maunium.net!
🔗That's all I know 🏁
See you next week, and be sure to stop by #twim:matrix.org with your updates!